CONFIGURING 802.1X WIRED SECURITY WITH WK12 & DELL SWITCH
This How to Article configures a Windows 2012 R2 NPS server as authentication from a Dell N2048 switch.
On Windows computers, if a user logs in to the domain with valid credentials whilst connected to the LAN it will enable internet / network connection, if the credentials are invalid it won’t connect to the network.
On computers running OS X you will have to put in a valid domain username and password for it to connect to the network.
Step-by-step guide
1. On the Dell Switch for Global Configuration:
authentication enable
dot1x system-auth-control
dot1x system-auth-control monitor
aaa authentication dot1x default radius
aaa authorization network default radius
radius-server host auth 192.168.0.X
primary
name “server_name“
usage 802.1x
key “your_radius_secret“
exit
radius-server host acct 192.168.0.X
key “your_radius_secret“
name “server_name“
exit
NB> 192.168.0.X should be changed to the NPS server which has your 802.1x policy on it, server_name should be changed to the FQDN of the NPS server and your_radius_secret should be the RADIUS secret you configured on your NPS server.
2. Configure the uplink port to have no forced authentication
interface Gi1/0/48
switchport access vlan 10
dot1x port-control force-authorized
exit
This line: dot1x port-control force-authorized is what forces the interface to be automatically authenticated.
NB> The uplink will need to not be forced to authenticate or your switch won’t be network accessible!
3. Configure authenticating ports.
interface Gi1/0/47
switchport access vlan 10
dot1x port-control mac-based
dot1x reauthentication
dot1x mac-auth-bypass
authentication order dot1x mab
exit
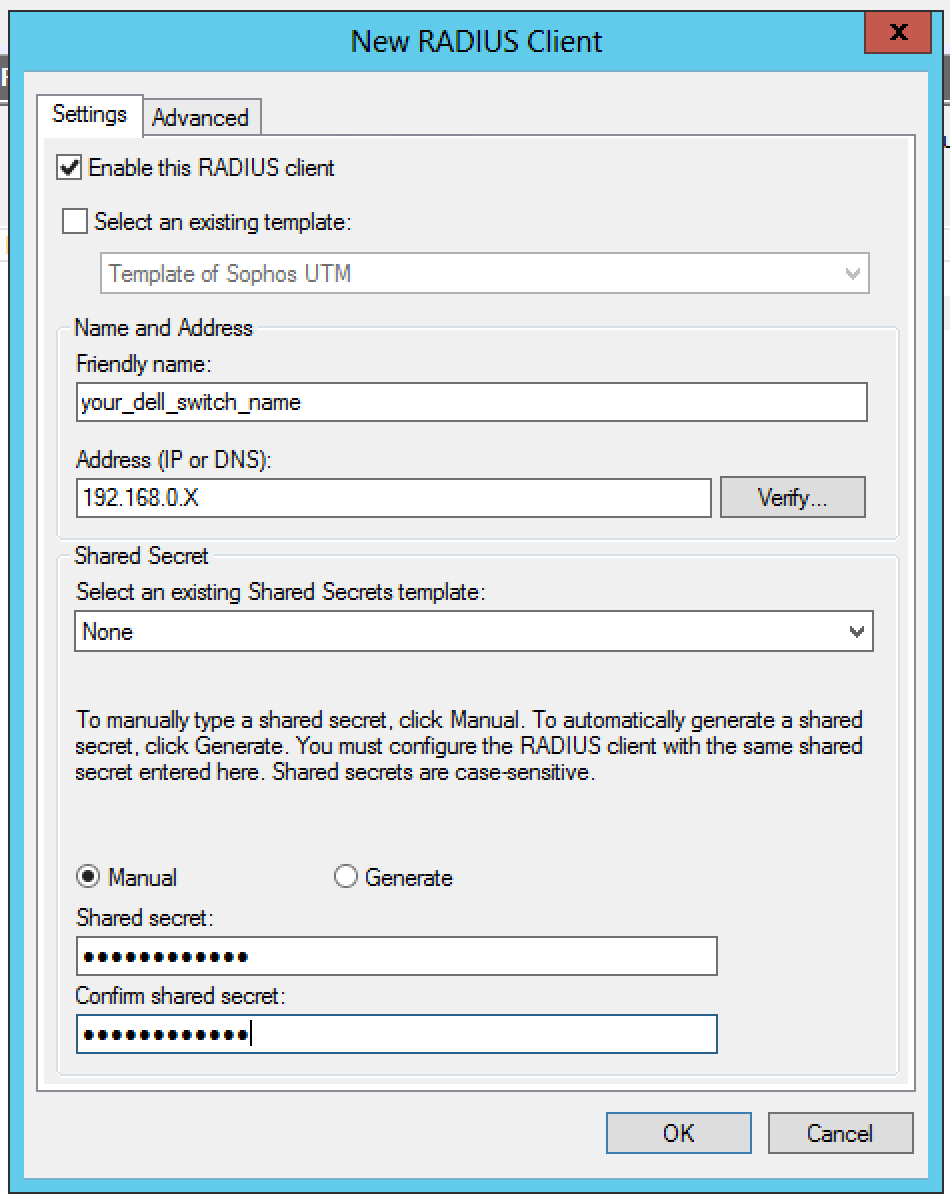
4. Configure the Radius client on the NPS server
Open NPS on the Server, right click on RADIUS Clients and Servers and Select New and fill in the information using your switch IP address as the Address (IP or DNS), and your_radius_secret which you stated earlier in the switch configuration.
5. Configure the NPS Network Policy
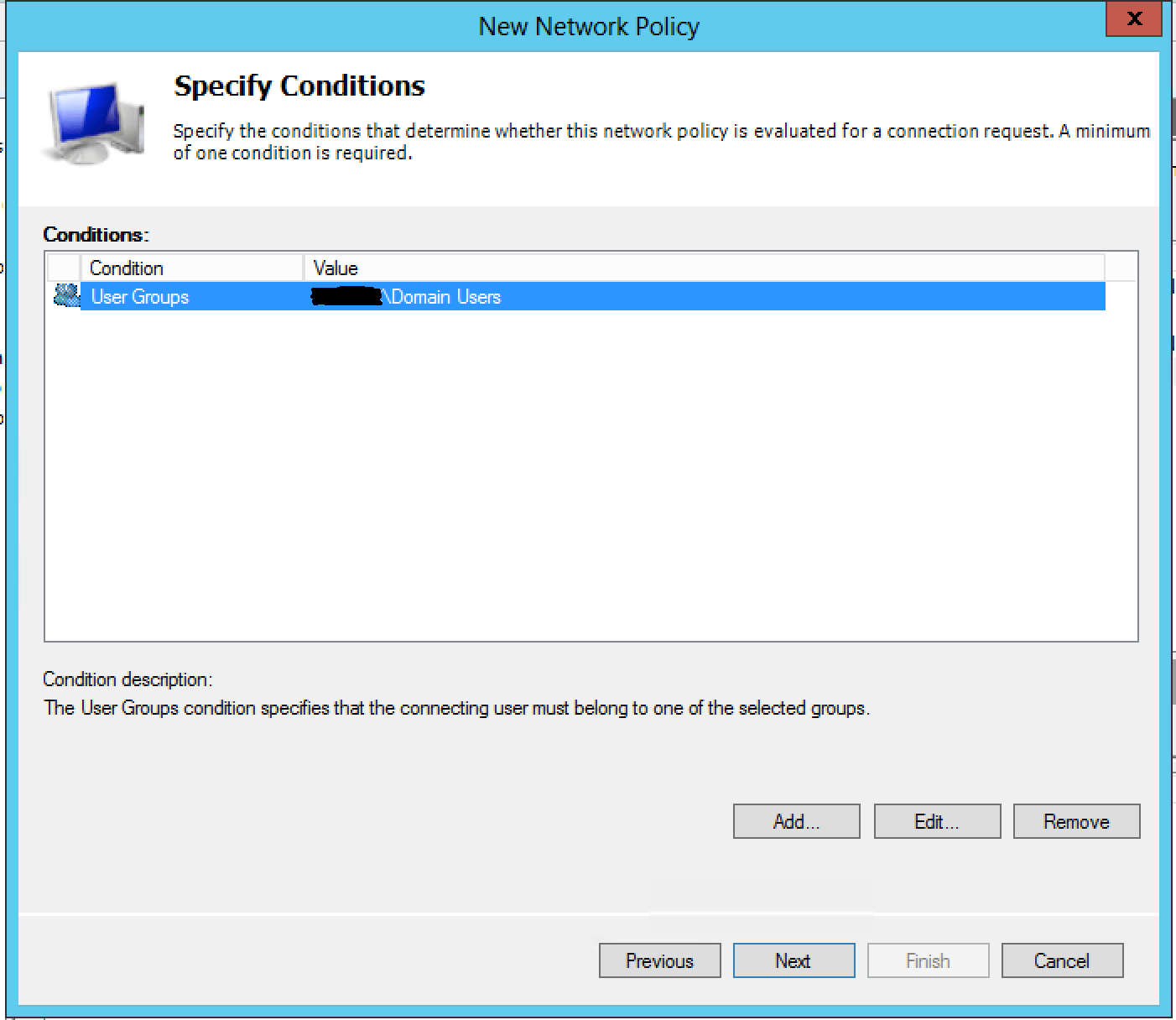
Again in NPS, Right click on Network Policies and Select New. These are the things you have to specify:
Type of network Access server: Unspecified.
Access Permission: Grant Access. Grant accessif the connection request matches the policy.
Conditions: Add your chosen Domain user Group which will be allowed to authenticate.
Constraints: Only authentication Methods need to be changed – see image 2:
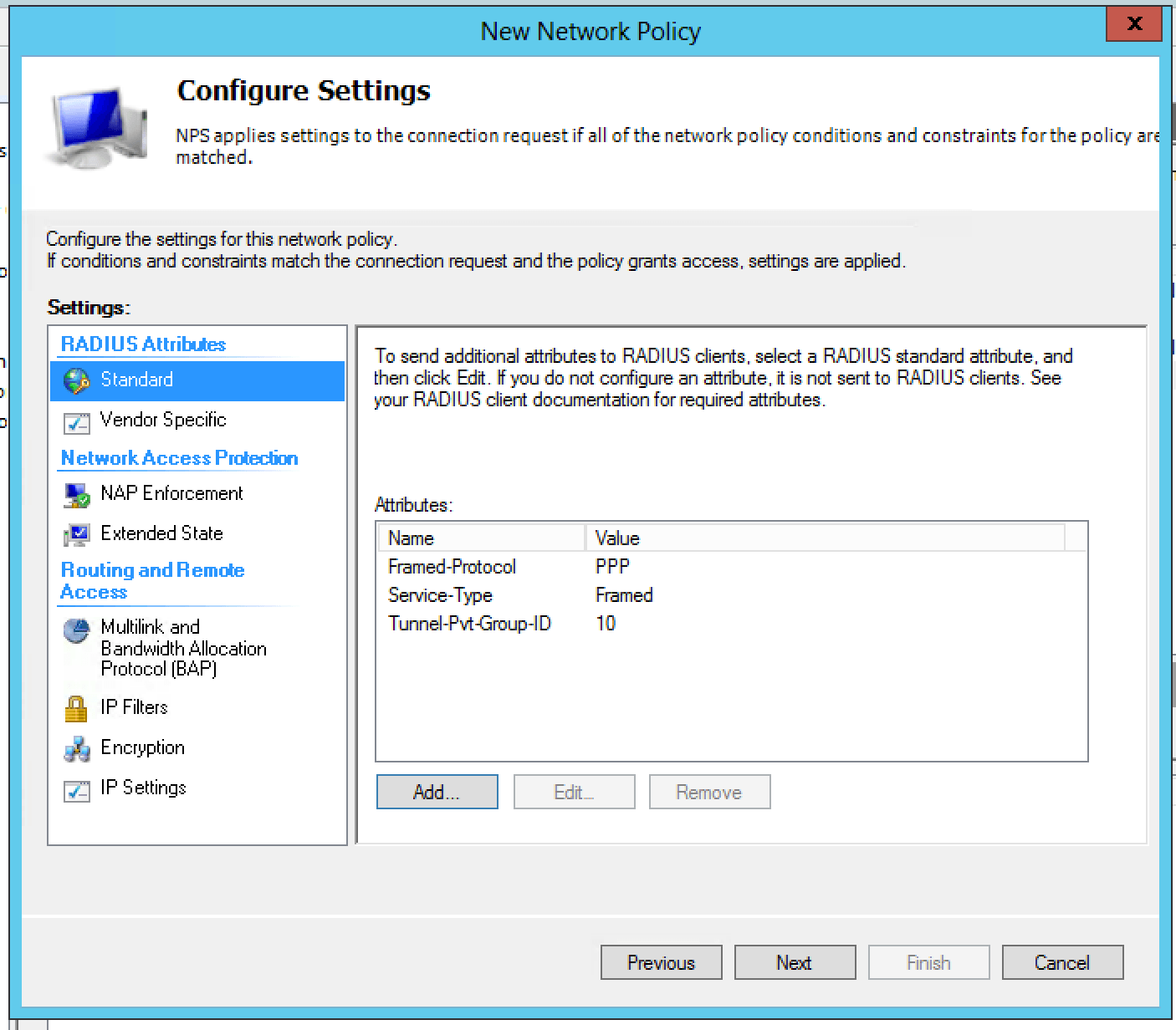
Settings: Radius Attributes > Standard. See Image 3:
NB> Tunnel-Pvt_Group-ID is the vlan ID on your switch, in this case VLAN 10.
802.1X should now be working properly.
One strange thing I noticed, if you login as a valid user and then logout and log back in as a non valid user it keeps the connection working. It reauthenticates periodically and at that point 802.1X will disconnect the client.
Add static MAC addresses to Interfaces of devices that can’t authenticate
Telnet to the switch and the enter configuration and run the following commands – in this case MAC address 001a.8c75.3ca8 on VLAN 10 is allowed through interface gi1/0/20 only.
conf
mac address-table static 001a.8c75.3ca8 vlan 10 int gi1/0/20

